PHP Security-How to Secure a PHP Based Website?

Do you have a PHP-based website? Then you just need to secure your website from cyber-attacks and hacks. Being a widely-used programming language for websites, PHP mostly remains under the threat of attacks and exploitation. In addition, the PHP programming language is very fragile, even a small bug or coding error can make your PHP-based website prone to cyber-attacks. So, while building your website with PHP language, it is very important to follow some PHP security guidelines so that you can strengthen the security of your website.
But the question is how to secure a website from hackers in PHP? Don’t worry! There are several tips to secure your PHP based website. So, no need to drop the idea of creating your website with this excellent programming language, rather read this blog to know how to stop hackers on your website.
Some Security Measures for PHP Based Website?
With the advancement of Digital Marketing Agency, cyber hackers also have invented smart hacking techniques, which make it necessary for business owners to rock-solid security for their websites. So, a PHP developer should be concerned about how to secure a website from hackers in PHP.
- Update PHP Regularly
It is important to update a PHP application to its newest version. Right now, PHP 8 has emerged as the latest version. So if you are still using the oldest version of PHP such as PHP 7 or 5.6, then you need to update it along with its code and functional logic like password, hashing, etc. There are some recommended tools available to help you update PHP such as PHP Compatibility Checker, PHP MAR, Phan.
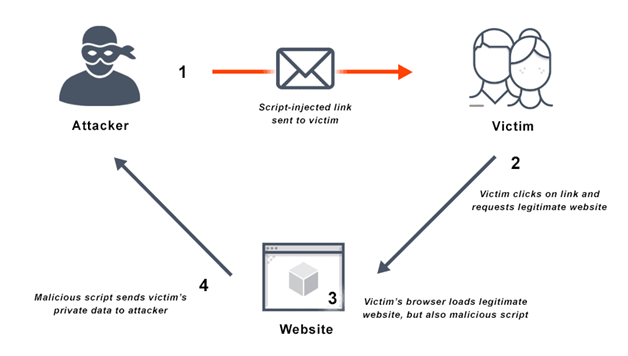
- Cross-site Scripting:
It is a type of malicious web attack, in which the hackers inject an external script into the website’s code. This type of attack most occurs in such places where users can put or submit data. It is one of the most complex external attacks that can affect the cores of your applications. Popularly known as an XSS attack, the infected code that is injected can replace the original code of your website.
But the question is how to stop hackers on your website from doing this type of cyber attack? The first that you have to do is to counter this attack by using HTML special chars & ENT_QUOTES in your application. By using these codes, you will be able to remove single and double quote options that will allow you to deal with XSS attacks.
- Session Hijacking:
It is such a cyber attack that can steal your session ID, by which hackers can gain access to the intended account. Thus hackers can validate your session by sending a request to the server.
To prevent this type of hacking it is recommended to bind your session to your IP address. Make sure your IDs are not exposed in any circumstances.
- SQL Injection Attacks
It is an attack in which hackers use particular URL parameters to get access to the database, thus they can perform several disasters in your website like deleting the entire database application.
If you want to prevent this type of cyber attack, it is better to use parameterized (PDO) queries, which will help you to secure your SQL queries and also make them able for processing.
Now look at how to check the login credential for authenticating the user inputs in the respective fields:
$uname=$_REQUEST[‘username’];
$pass=$_REQUEST[‘password’];
$mysql_query(“select * from users where username='”.$uname.” and password='”.$pass.” ’ ” );
Again, in an unusual scenario instead of entering the username and password you can enter a value like the following:
Username=’ or ‘1’=’1 Password= ‘ or ‘1’=’1 In such a case, the user query will be like this: 1 select * from users where username=” OR ‘1’=’1′ and password=” OR ‘1’=’1′
- Use SSL Certificates
If you want to get a one-stop solution of secure data transmission over the internet, always use SSL Certification which is a globally recognized protocol.
- Hide Files from the Browser
With the help of the directory structure in the micro PHP frameworks, you can ensure the storage of your important framework files like controller, models, the configuration file, etc.
Conclusion:
PHP is the most powerful server-side language used by more than 79% of the world’s web including some top content management systems like eCommerce and WordPress. Again, the PHP programming language is used by some of the most popular websites including Facebook, Wikipedia. So if you want to build an exclusive website that can help you to grow your business more efficiently, hire the expected developers of the PHP development company who have extensive knowledge of how to stop hackers on your website.
FAQs:
1. Hire Digital Infoways as a PHP development company?
Digital Infoways is a leading name among the PHP development service provider companies. They guarantee that no compatibility problems will occur while taking the PHP services from them. Thus they can satisfy your business goal easily by providing PHP development services at an affordable price.
2. What are the Statistics about PHP Cyber Attacks in recent years?
Here look at some statistics that show the vulnerability of PHP based websites include
- WordPress uses PHP as its scripting language. The study shows that more than 35% of websites use WordPress and are subjected to the highest numbers of vulnerabilities. In 2018, WordPress shows 542 vulnerabilities.
- According to a report, SQL Injection and XSS attacks are the most common attack techniques on a PHP-based website.
- It is proved that hackers can steal about 75 records every second.
- In 2019, the attack rate was very high. There was an attack every 39 seconds.
- 3. How does it cost to hire a PHP development service?
The cost of PHP development services depends on several factors such as the cost of hiring a PHP development company, the functionalities, strategy, maintenance, etc.
4. How secure is PHP?
PHP is secure as any other major language.
5. What are PHP vulnerabilities?
PHP object Injection is a kind of app-level vulnerability that can cause several malicious attacks.